
DNV suggested some companies may hesitate to invest in cybersecurity because most respondents believe their organization has so far avoided a major cyberattack. (Source: Shutterstock.com)
While many energy professionals believe cyberattacks could cause harm in the next two years, investments in security aren’t necessarily being made.
Concerns about the security around operational technology (OT) have escalated, particularly since the 2021 ransomware attack on the Colonial Pipeline. Even so, one of the challenges is what appears to be a “wait and see” approach to OT cybersecurity, according to DNV’s “The Cyber Priority: The state of cyber security in the energy sector” report published on May 19.
Chief among the actions energy companies need to take are allocating sufficient funds to cybersecurity and training as well as knowing what the OT vulnerabilities are, said Trond Solberg, managing director of cybersecurity at DNV.
“It is concerning to find that some energy firms may be taking a ‘hope for the best’ approach to cybersecurity rather than actively addressing emerging cyber threats.”—Trond Solberg, managing director, cybersecurity, DNV
The research, carried out in February and March, surveyed more than 940 energy professionals involved in a range of functions within the industry, including those with in-depth knowledge of cybersecurity, engineers, general managers and C-suite executives. Respondents were in Europe, the Americas, the Middle East and Africa, and Asia Pacific.
The results of the research “confirmed a suspicion we had,” Solberg said.
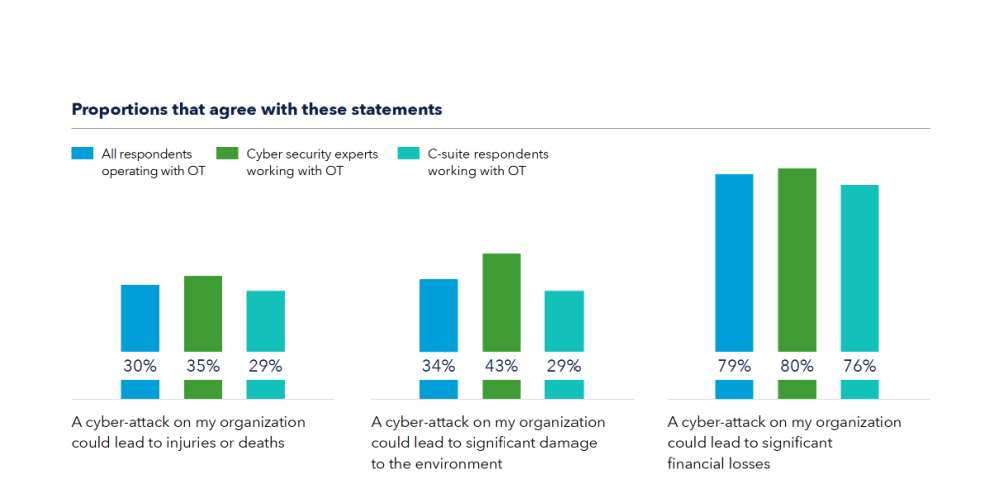
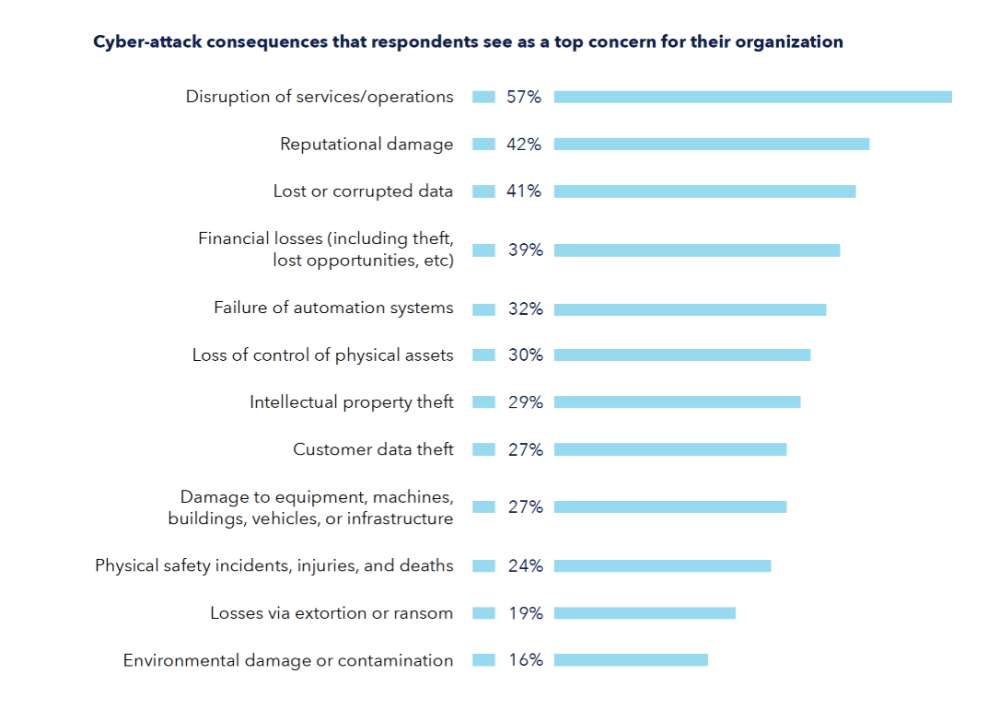
The research revealed that energy professionals believe that cyberattacks on the industry are likely to cause harm to life, property and the environment in the next two years, with 85% of respondents expecting an attack to cause operational shutdowns, 84% expecting physical damage to assets, 74% expecting an attack to harm the environment and 57% anticipating loss of life.
DNV raised concern about two other results. Only 47% of respondents believe the security of their operational technologies (OT)—the control systems managing, monitoring and controlling industrial operations—is as robust as their IT security, and 44% of the industry’s C-suite executives see the need for urgent improvements to prevent a serious attack on their business, despite emerging threats.
Solberg said the consequences of OT attacks are “much higher” than those around information technology (IT) and info security attacks.
“Unlike information security, with OT there are physical consequences,” which could include pollution, accidents and damage to life and property, he said.
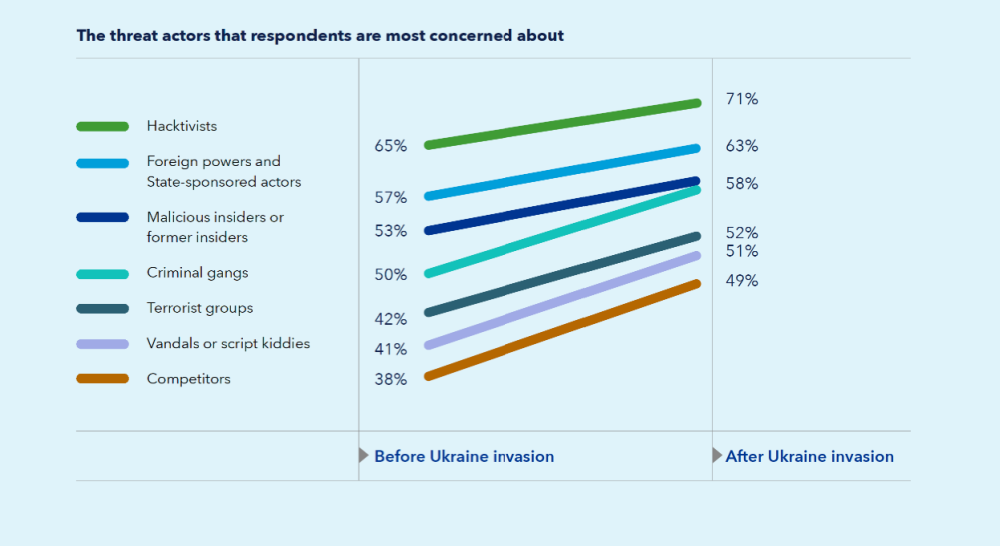
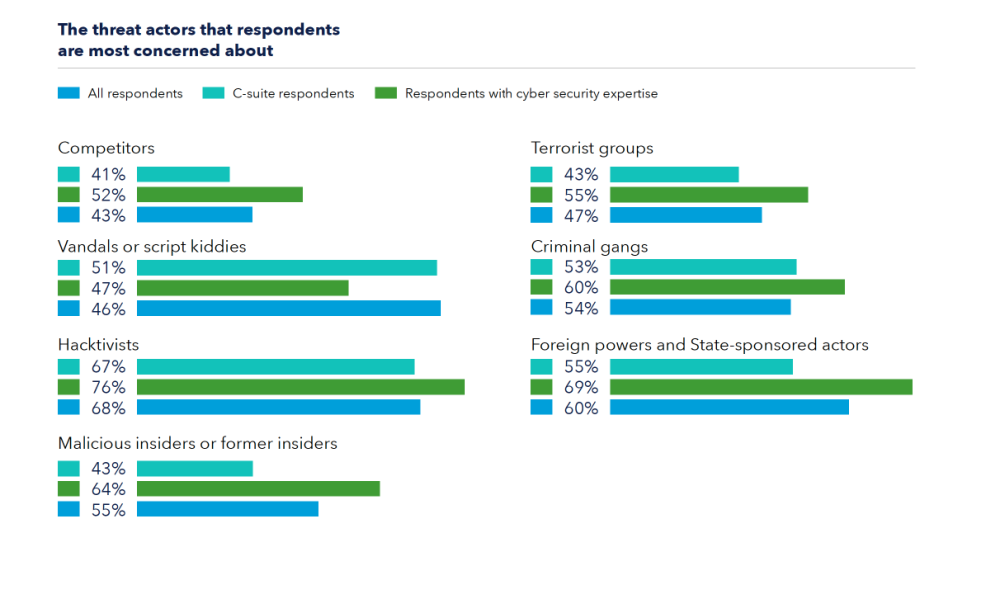
The concern, he added, is that attacks are becoming more sophisticated and seeking results beyond what can be achieved with ransomware.
“As OT becomes more networked and connected to IT systems, attackers can access and control systems operating critical infrastructure such as power grids, wind farms, pipelines and refineries,” he said.
What makes this particularly worrisome is the fact that the industry hasn’t made the necessary investments to defend against OT cyberattacks, Solberg said.
“The maturity of the energy business is not where it should be in terms of investment,” he said.
Instead, Solberg added, it appears the industry is taking a “wait and see” attitude.
The research revealed that 44% of C-suite respondents believe they need to make urgent improvements in the next few years to prevent a serious attack on their business, and 35% of energy professionals say their company would need to be impacted by a serious incident before investing in their defenses.
“It is concerning to find that some energy firms may be taking a ‘hope for the best’ approach to cybersecurity rather than actively addressing emerging cyber threats. This draws distinct parallels to the gradual adoption of physical safety practices in the energy industry over the past 50 years,” Solberg said.
DNV suggested some companies may hesitate to invest in cybersecurity because most respondents believe their organization has so far avoided a major cyberattack and only 22% suspect their organization has been subject to a serious breach in the last five years.
“We need to fight the wait and see attitude,” Solberg said.
Most important for energy companies, he said, is for companies to devote more attention to cybersecurity, particularly from the outset of projects. The industry took this approach with safety, and over decades the safety of the industry improved, he said.
“Through major incidents, the sector matured their safety work. The discipline now spans through the full lifetime of the project, from start to finish,” Solberg said. “That’s the kind of discipline we need for OT cybersecurity.”
The investments in OT cybersecurity should ideally start with the beginning of each project, he said. He noted retrofitting equipment for OT cybersecurity is possible, particularly given the longer life spans of expensive energy industry equipment, “it’s never as good as if you started a project in the right way.”
If companies don’t have the expertise in-house, Solberg urged the companies to seek outside expertise.
And while companies are working to strengthen their OT cybersecurity programs, they need to invest in supply chain security as well.
“Energy companies can have complete oversight of their own vulnerabilities and have all the right measures in place to manage the risk, but that won’t make a difference if there are undiscovered vulnerabilities in their supply chain,” said Jalal Bouhdada, founder and CEO at Applied Risk, an industrial cybersecurity firm DNV acquired in 2021. “Our research identifies ‘remote access to OT systems’ among the top three methods for potential cyberattacks on the energy industry. We would urge the sector to pay greater attention to assuring that equipment vendors and suppliers demonstrate compliance with security best practice from the earliest stages of procurement.”
What is worrisome, Solberg said, is that only 28% of energy professionals working with OT said their company is making the cybersecurity of their supply chain a high priority for investment, compared to 45% of OT-operating respondents who say expenditure in IT system upgrades is a high investment priority.
Not only do companies need to know where they’re vulnerable, Solberg said, but they also need to invest in both defensive technology and training personnel on cybersecurity methods.
Only 31% of respondents said they knew what to do in the face of a potential cyber risk or threat.
“A company’s workforce is its first line of defense against cyberattacks,” Bouhdada said, adding that effectively training the workforce “can make all the difference to safeguarding critical infrastructure.”
So while companies may be aware of the need to invest in the technical side to defend against cybersecurity attacks, Solberg said, it is also “very important to train people to get the right awareness around OT security.”
Recommended Reading
E&Ps Pivot from the Pricey Permian
2025-02-01 - SM Energy, Ovintiv and Devon Energy were rumored to be hunting for Permian M&A—but they ultimately inked deals in cheaper basins. Experts say it’s a trend to watch as producers shrug off high Permian prices for runway in the Williston, Eagle Ford, the Uinta and the Montney.
Ring May Drill—or Sell—Barnett, Devonian Assets in Eastern Permian
2025-03-07 - Ring Energy could look to drill—or sell—Barnett and Devonian horizontal locations on the eastern side of the Permian’s Central Basin Platform. Major E&Ps are testing and tinkering on Barnett well designs nearby.
E&P Highlights: Jan. 21, 2025
2025-01-21 - Here’s a roundup of the latest E&P headlines, with Flowserve getting a contract from ADNOC and a couple of offshore oil and gas discoveries.
Hibernia IV Joins Dawson Dean Wildcatting Alongside EOG, SM, Birch
2025-01-30 - Hibernia IV is among a handful of wildcatters—including EOG Resources, SM Energy and Birch Resources—exploring the Dean sandstone near the Dawson-Martin county line, state records show.
Sabine Oil & Gas to Add 4th Haynesville Rig as Gas Prices Rise
2025-03-19 - Sabine, owned by Japanese firm Osaka Oil & Gas, will add a fourth rig on its East Texas leasehold next month, President and CEO Carl Isaac said.
Comments
Add new comment
This conversation is moderated according to Hart Energy community rules. Please read the rules before joining the discussion. If you’re experiencing any technical problems, please contact our customer care team.






